Too many Authenticator codes?
I remember adding my first Time-based One Time Password (TOTP) into Google Authenticator. It was cutting edge and a pinnacle of security. Recently though, everything seems to want MFA (Multi Factor Authentication) and my list of Authenticator codes stretches over 3-pages long. It is inefficient, and I hate needing to grab my phone each time I want to log on. Not only that but I have multiple Authenticator apps, which makes the problem worse.
In this post I share a way to securely streamline your workflow, ensure you can access your codes from anywhere, and not get locked out if you lose your phone.
You might not realise it, but today's password managers are also authenticators, and they'll secure your MFA keys with the same level of security as your passwords. They’ll make your codes accessible right alongside your passwords, on all your devices, and many of them will auto-fill the MFA box too. Easy. You can replace Google Authenticator!
Is it safe to store 2FA in a password manager?
The biggest reason to keep your 2FA tokens in your password manager is that it's in one location and gets backed up. Far too many people don't realize that apps like Google Authenticator and many others don't automatically backup your 2FA tokens. So, if you get a new phone or lose your phone, you also lose your 2FA.
It can be argued that by storing both your passwords and 2FA in one place you turn your secure two factor authentication method into a single factor — the password manager. The argument is that any malicious actor who gets access your password manager now has access to both factors needed to log into their accounts.
That is true; however, that argument assumes that the 'two factorness' of a 2FA key is the most important security element and ignores that TOTP keys stand for an unguessable long-term secret that isn’t transmitted during logon. Using 2FA protects you from password guessing attacks, and captured password attacks regardless of where you store your 2FA information.
It’s important to evaluate what you really get out of 2FA. Storing it in your password manager strikes a good balance between security and convenience; however, if the two factorness of 2FA is most important to you then don’t do this.
Be careful of browser extensions
It's important to know about browser extension authenticators. I’ve seen many people use browser these to manage their 2FA keys. Be careful.
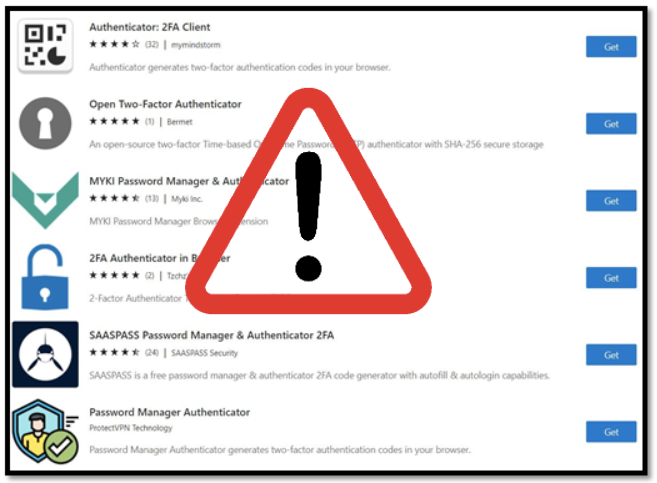
You should know that most of them don’t encrypt your long-time secret and leave it unsecured in your web browser’s data store. Technical information about how this type of storage works is here. Be aware too that if your browser synchronises settings across all your devices your unsecured 2FA long-term key will be copied all over the place too.
Final words
If you don’t already use a password manager, then you should. I’ve tried 1Password, LastPass, and now use Bitwarden. It’s open source and can be totally free although you need the US$10 per annum Premium version to store 2FA keys but it's well worth it. You get 1GB of storage to store all sorts of stuff like photos of your passport, drivers license and credit cards. 80% Scottish heritage makes me pretty value-based in my decision making but I’m all good with this.
If you're already using a password manager, consider using it to manage your 2FA/TOTP keys too. Maybe this post is enough to tip you over the edge.
